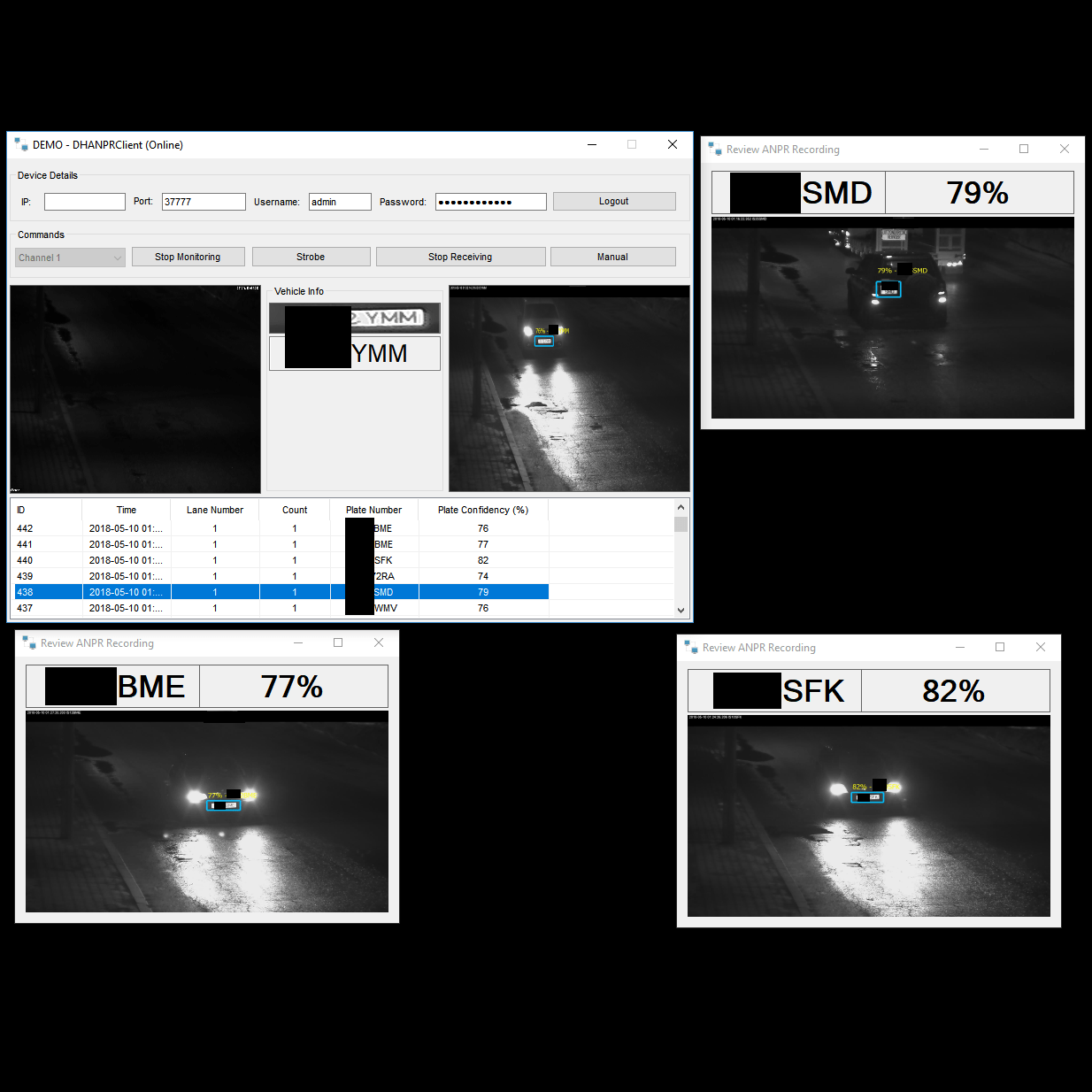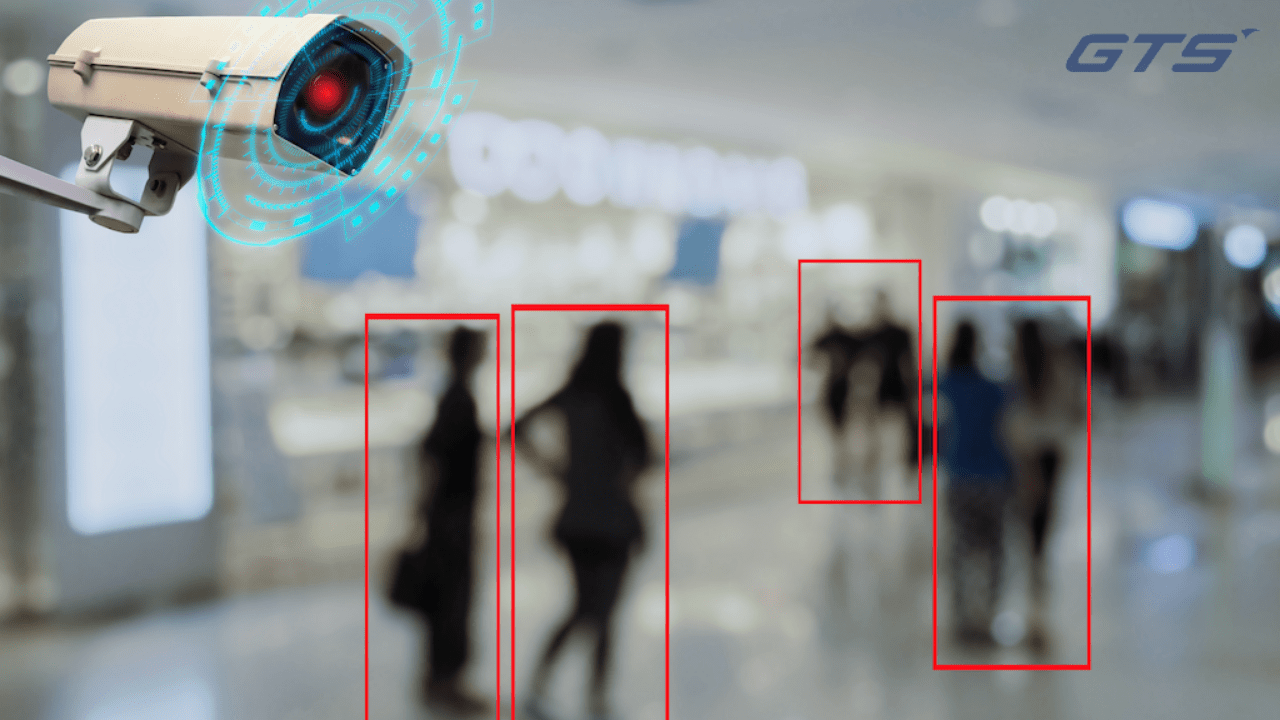
In the ever-evolving landscape of technology, the convergence of surveillance systems, Artificial Intelligence (AI) and software development has opened up a realm of possibilities. One such avenue is the utilization of DAHUA’s own SDK (Software Development Kit) and devices, which serves as a gateway for AI providers to integrate their own cutting-edge AI algorithms into the solutions provided to their clients, in a B2B matter. This advancement not only enhances security measures but also paves the way for innovative applications across various industries.
Continue reading EVOSEC, DAHUA and AI solutions